Main Technologies
MetaDefender Core allows you to detect, analyze and eliminate malwares and Zero-day attacks with the combination of 4 main cutting-edge threat prevention and detection technologies:
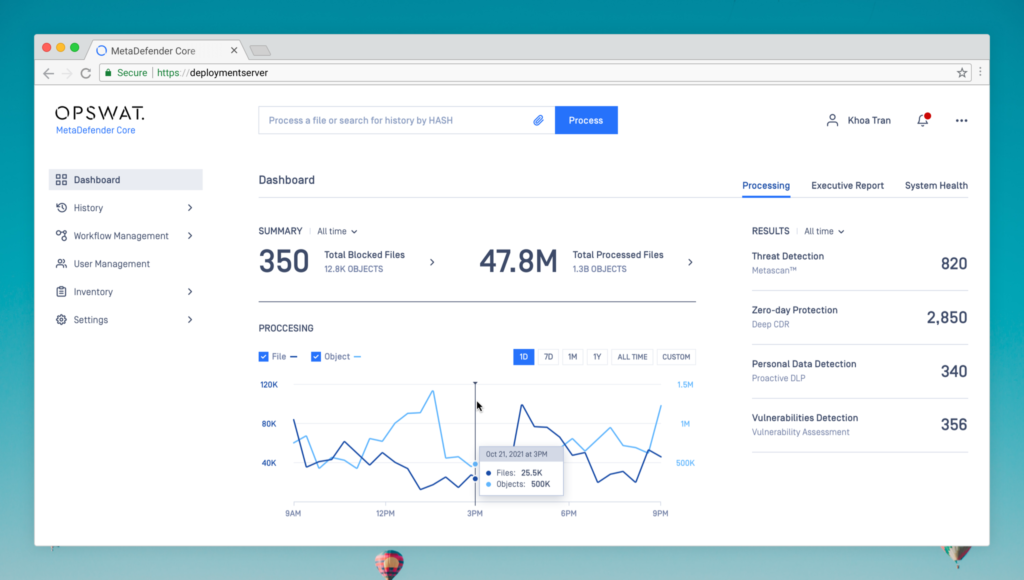
- Multi-Scanning: Scans files with 30+ antimalware engines to detect over 99% of known malwares.
- Deep Content Disarm & Reconstruction: Recursively sanitizes files and their embedded objects to remove potential threats.
- Proactive Data Loss Prevention: Removes, redacts or watermarks sensitive data before it enters or leaves your organization.
- Vulnerability Assessment: Uncovers vulnerabilities in installers, binaries or applications before they are installed.
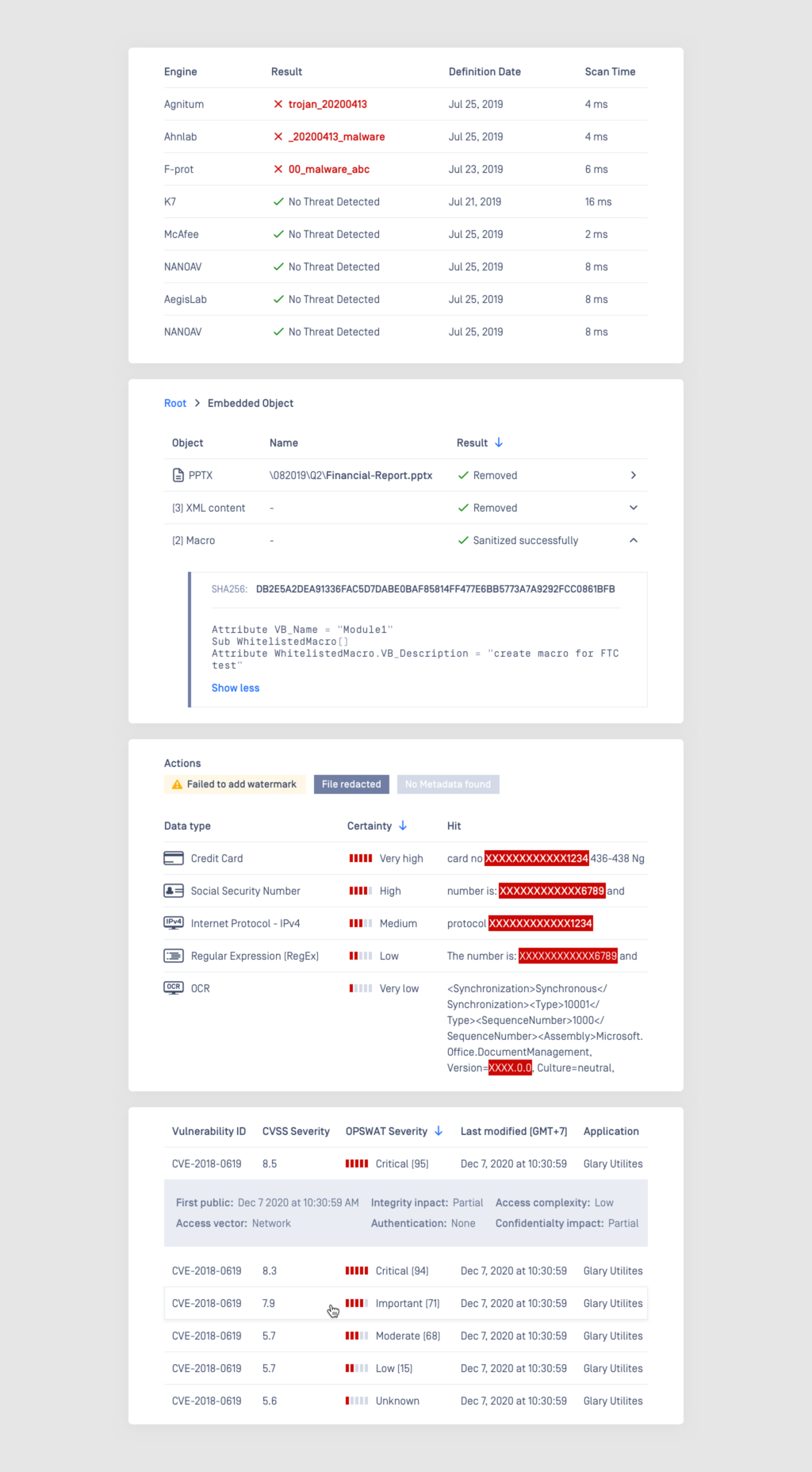
File Type Verification
To bypass security mechanisms, a file’s extension can be changed to spoof the operating system and users without modifying the content or changing the capability of the file. File Type Verification identifies a file based on its actual content, not the unreliable extension.
File Type Verification currently supports 4,500+ file types.
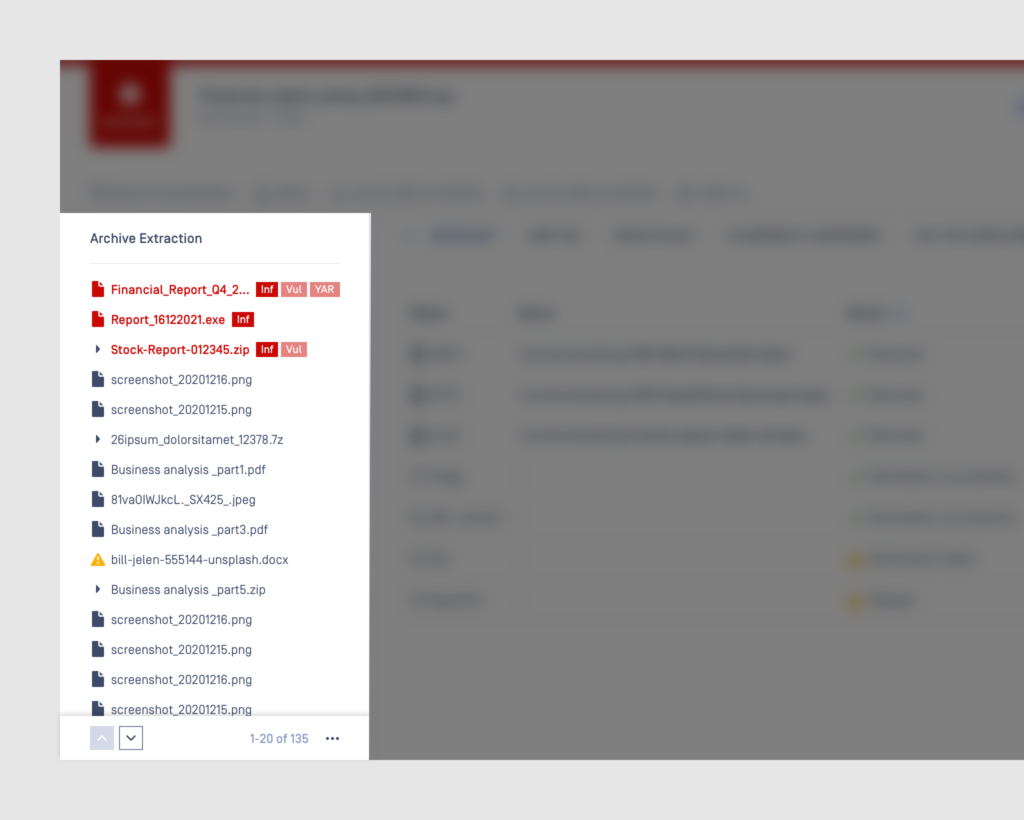
Zip Bomb Attack Prevention
Extracting and scanning an archive file using Archive Extraction engine prevents zip bomb attack by detecting and block it in advance. The engine also supports scanning of both extracted and unextracted file, which improves detection rate and decrease scanning time.
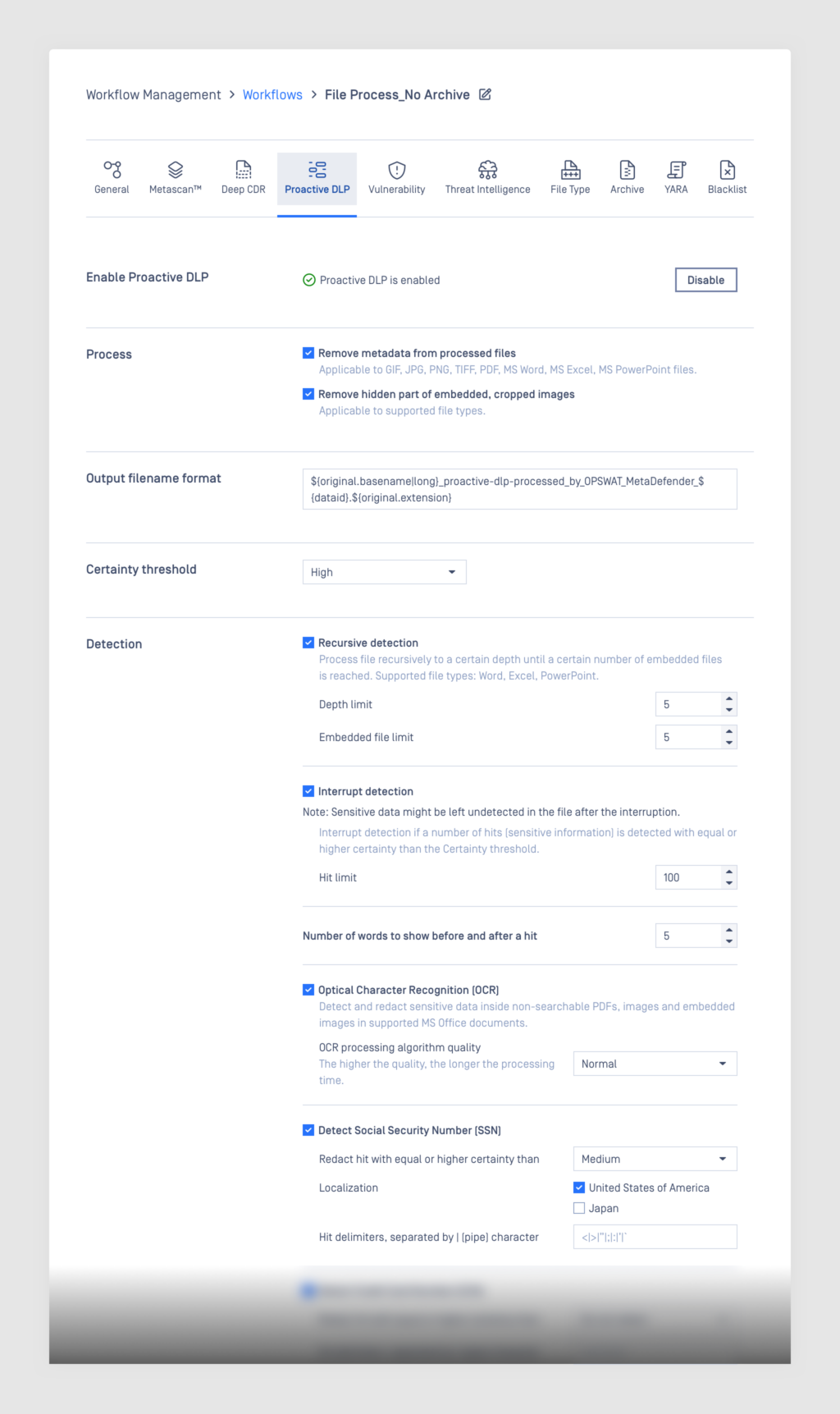
Workflow Customization
MetaDefender Core can work as an integration into existing IT infrastructure or a stand-alone solution. Both deployment methods require flexibility to serve multiple use cases and purposes. Workflow customization allows administrators to create multiple workflows to handle different security policies based on their unique requirements.
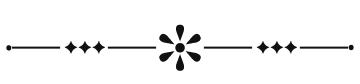
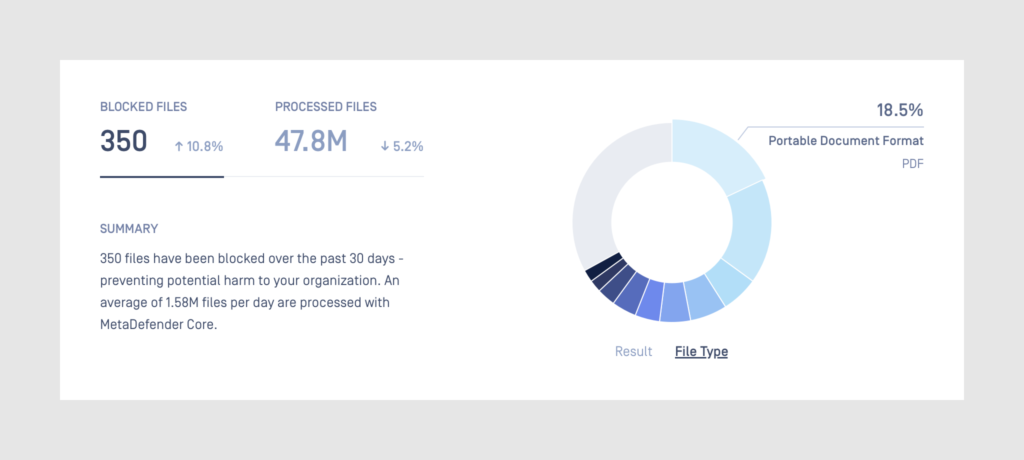
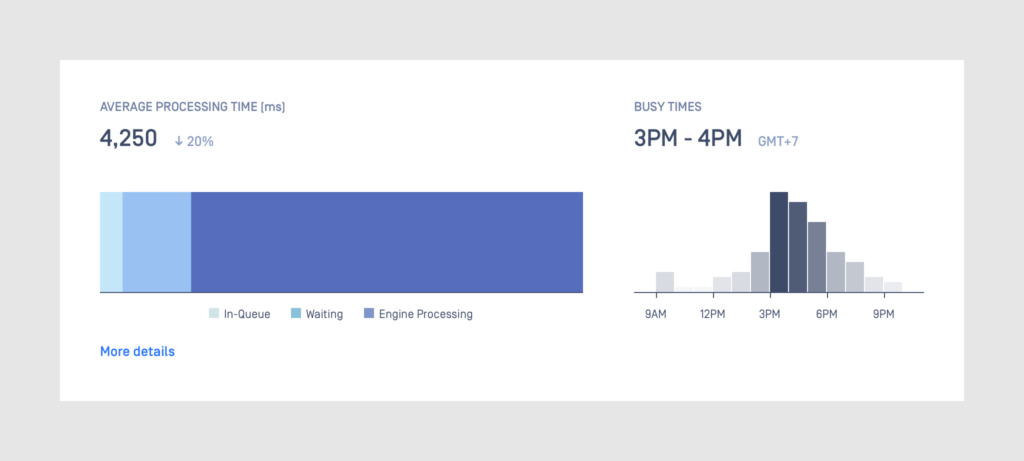
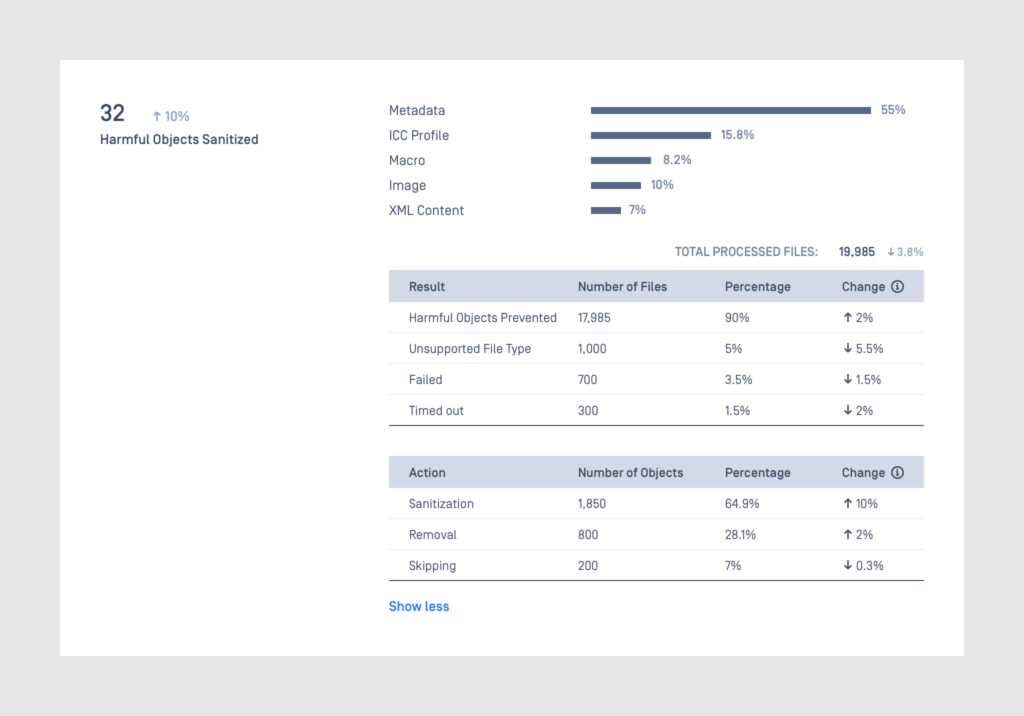
Deep Insights with Executive Report
MetaDefender Core gives detailed reports for administrators and data scientists to monitor current operations, analyse history, predict and make precise decisions.
Module Update
Each module constructing the system can be updated manually or automatically, keeping the system healthy and up-to-date.
Installation
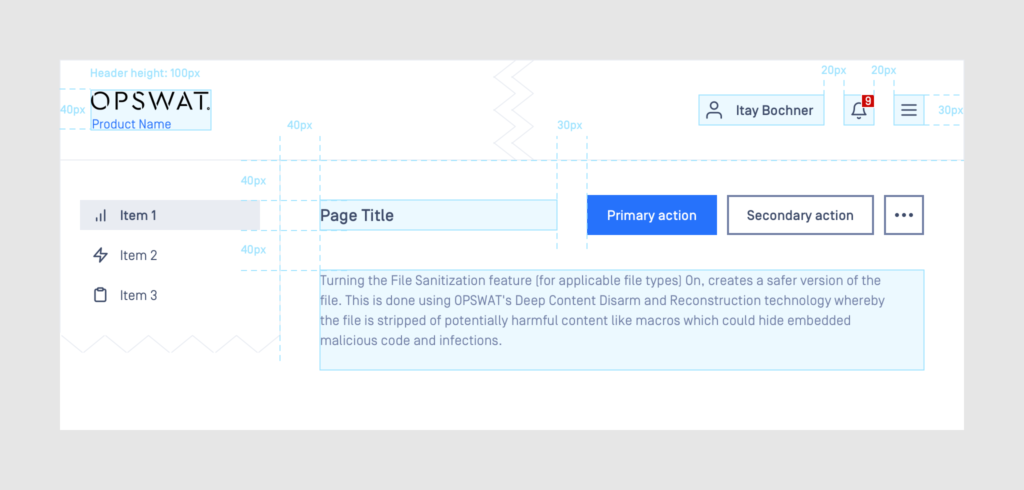
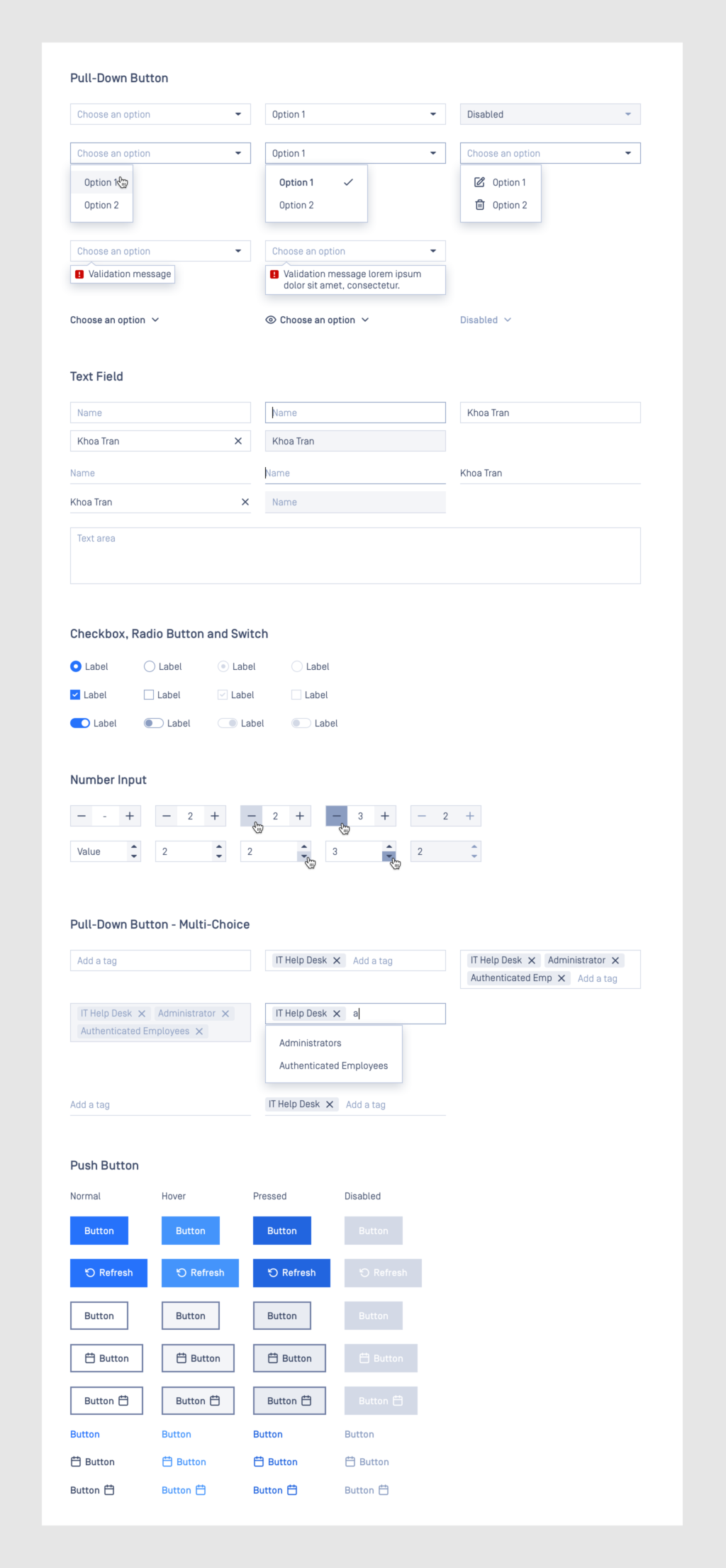
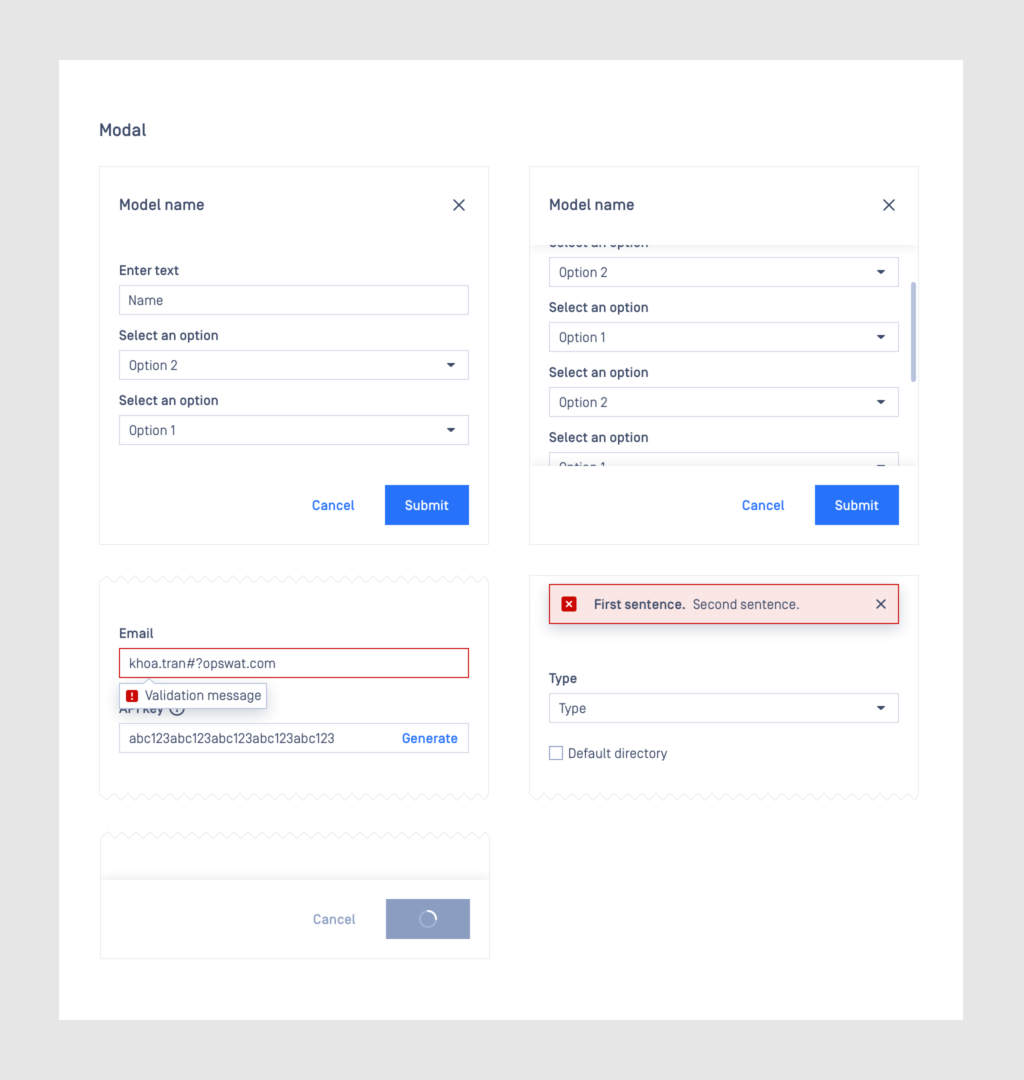
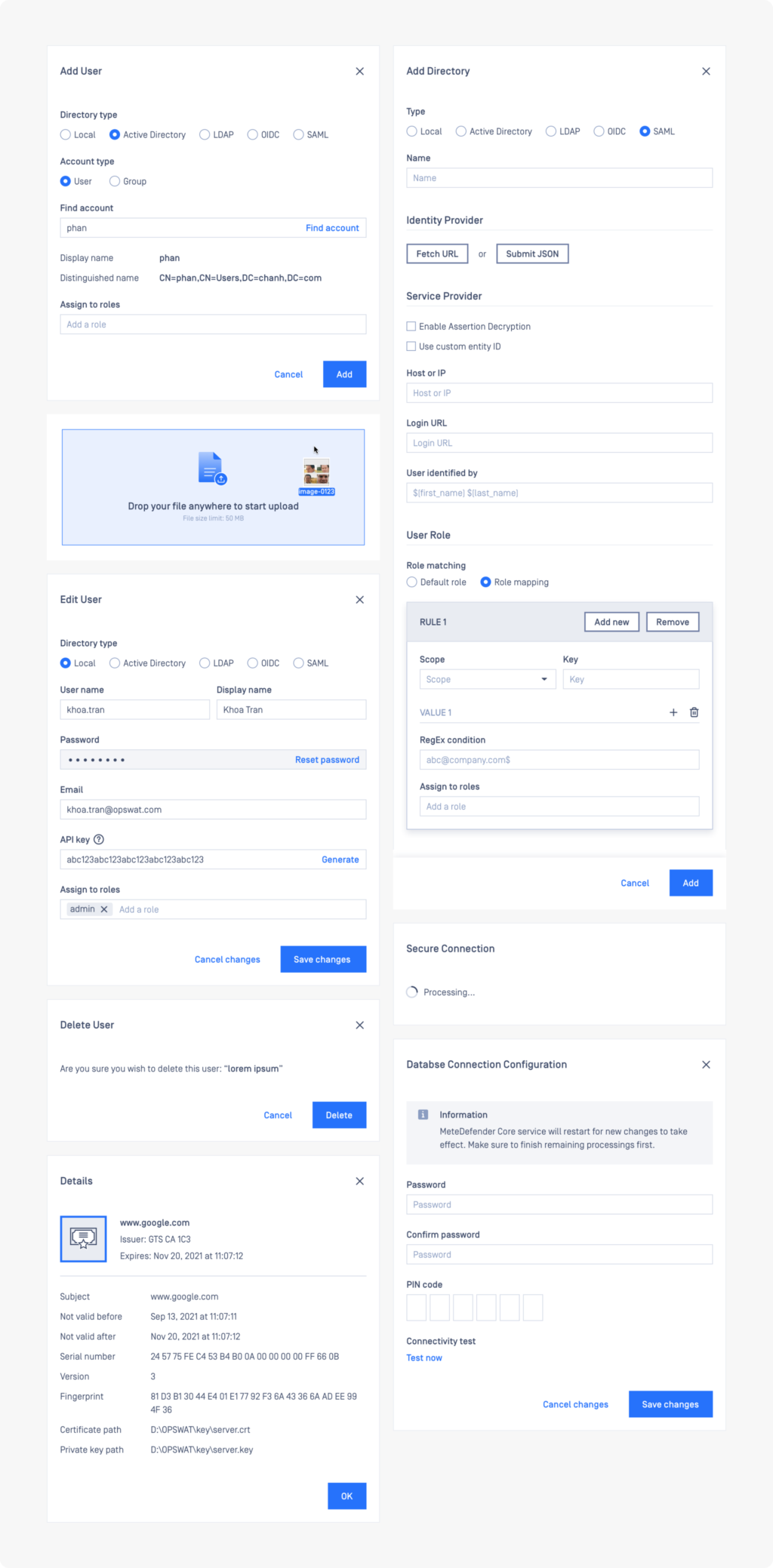
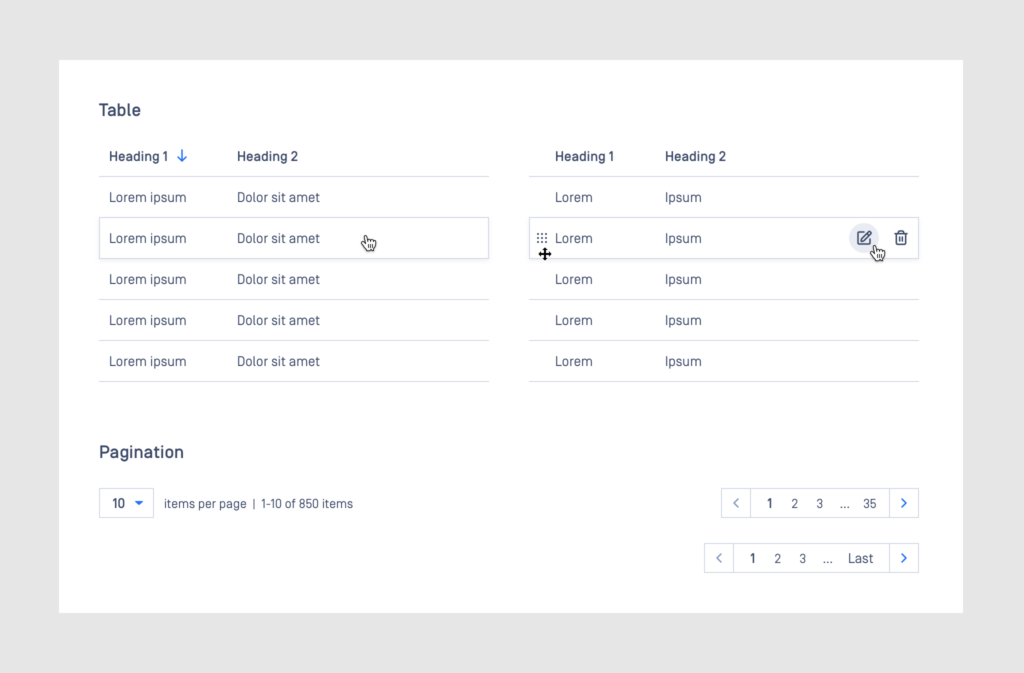
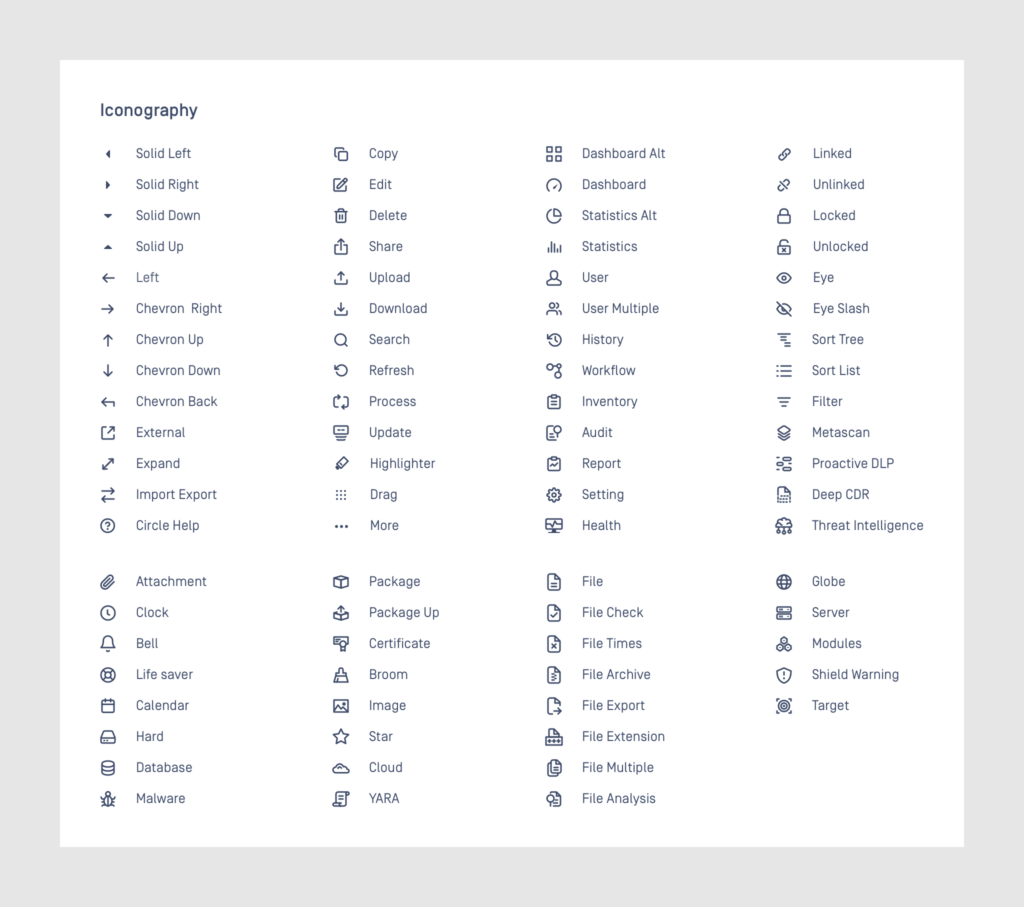
Design System
One of the biggest challenges in the design process was to bring complex raw data straight from backend to a user-friendly interface. Despite being targeted for professional IT folks, some of the main goals of the design were to create a product that was intuitive and easy to operate.
Trust
MetaDefender Core is trusted by governments and world-leading companies from vast range of industries including nuclear energy, military and cybersecurity.